Configure Azure AD connector
- 27 Oct 2023
- 3 Minutes to read
- Print
- DarkLight
- PDF
Configure Azure AD connector
- Updated on 27 Oct 2023
- 3 Minutes to read
- Print
- DarkLight
- PDF
Article summary
Did you find this summary helpful?
Thank you for your feedback
Steps to configure the connector:
- Login to Cross Identity and go to the admin console.
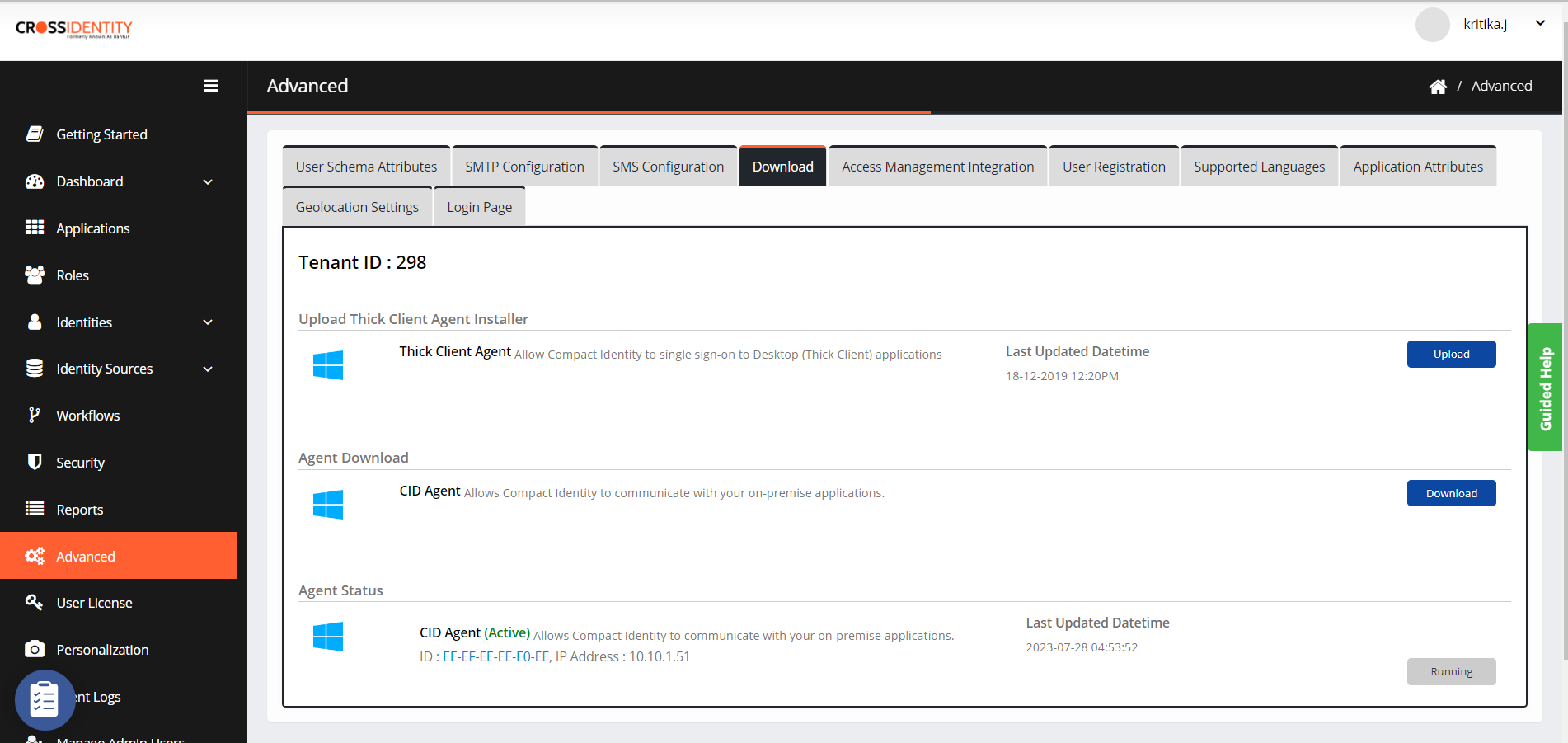
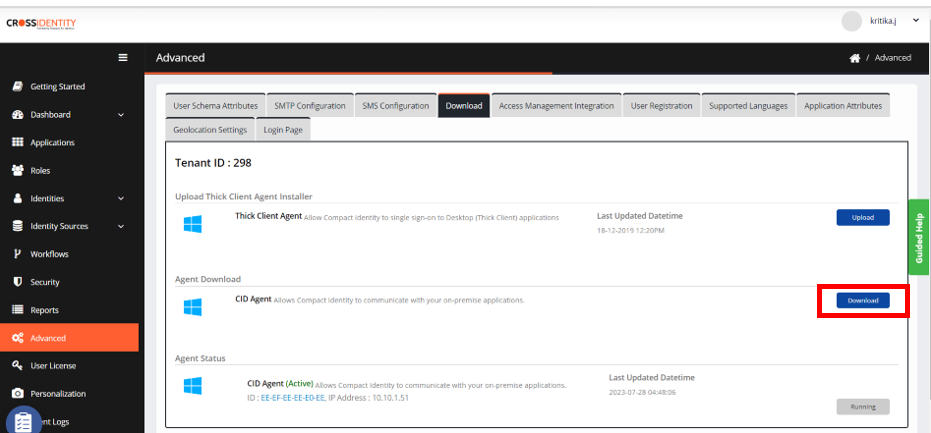
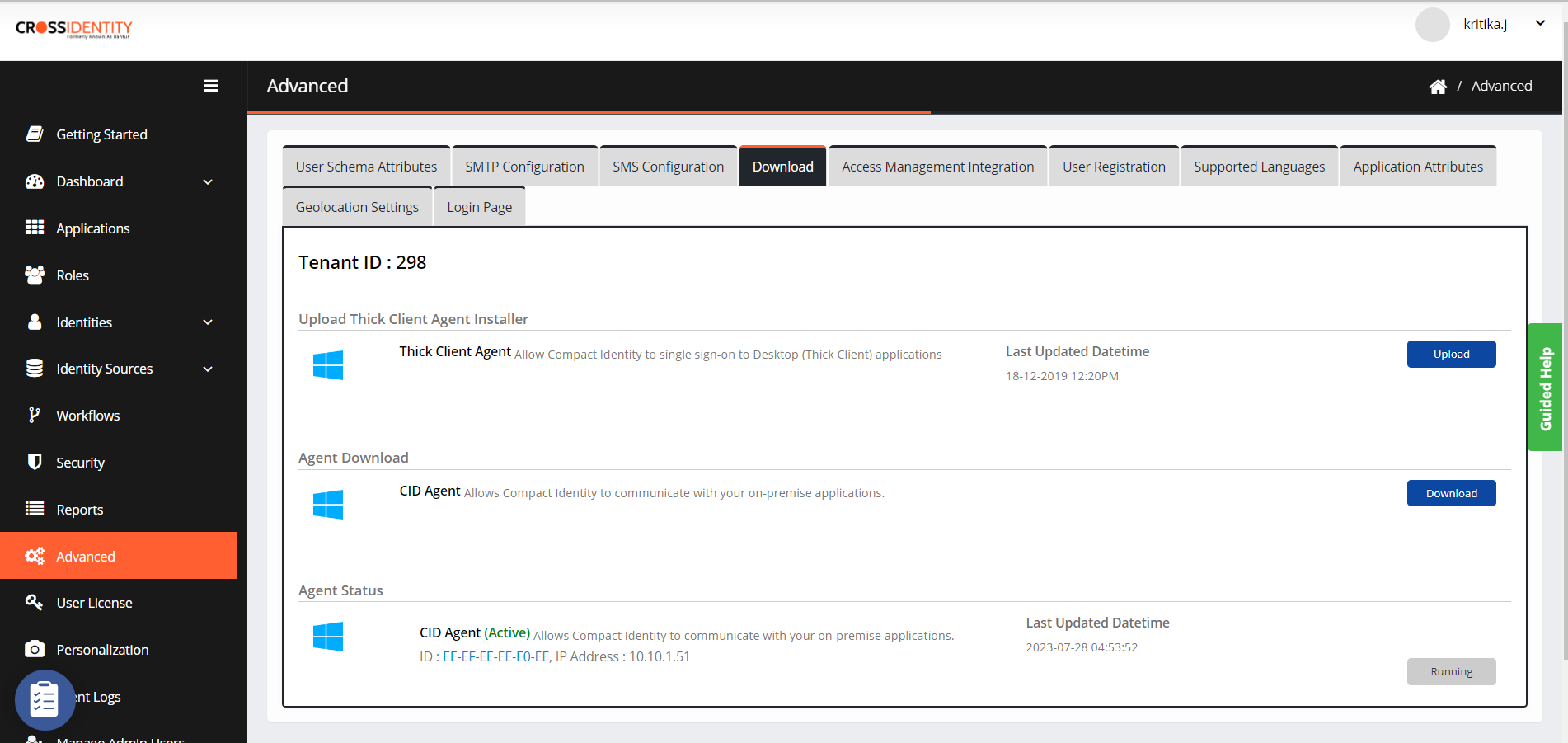
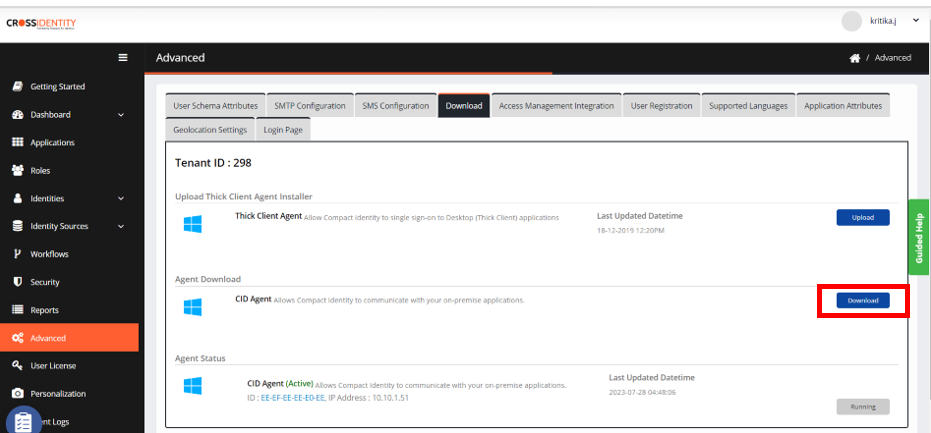
Download the CID Agent file
- Click Advanced > Download.
- Click Download from CID Agent as highlighted in the image.
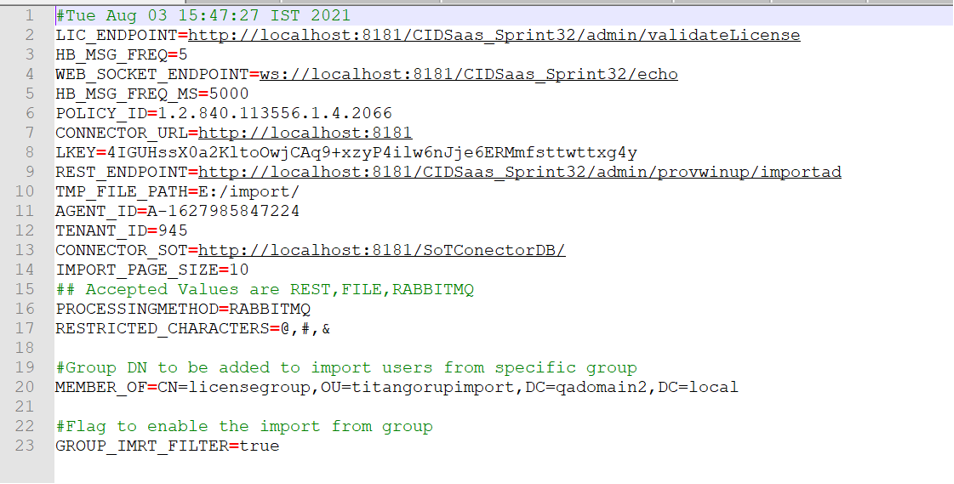
- After downloading the CID Agent, navigate to C:\Program Files\Apache Software Foundation\Tomcat 9.0\webapps\CIDAgent\WEB-INF\classes and verify the parameters.properties file.
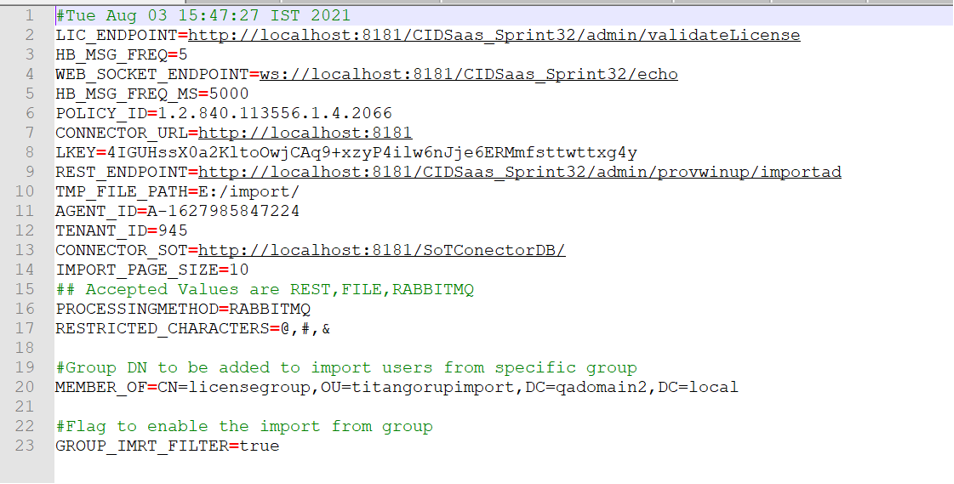
- Make changes for LIC_ENDPOINT, WEB_SOCKET_ENDPOINT, and REST_ENDPOINT as per the tenant URL received for CI.
- Make changes for CONNECTOR_URL, and CONNECTOR_SOT as per the agent URL.
To utilize the RabbitMQ feature, mention PROCESSING METHOD as RABBITMQ. If not required then mention REST. - After making the necessary changes save the file.
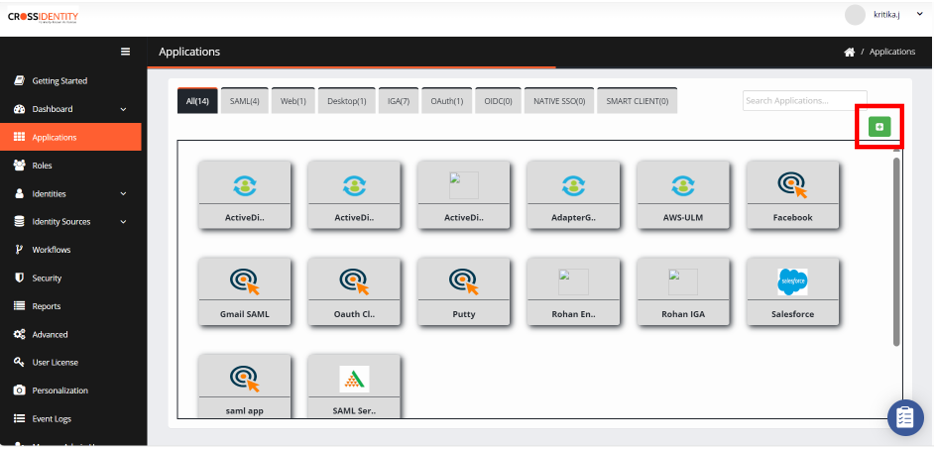
Onboard AzureAD application in CI
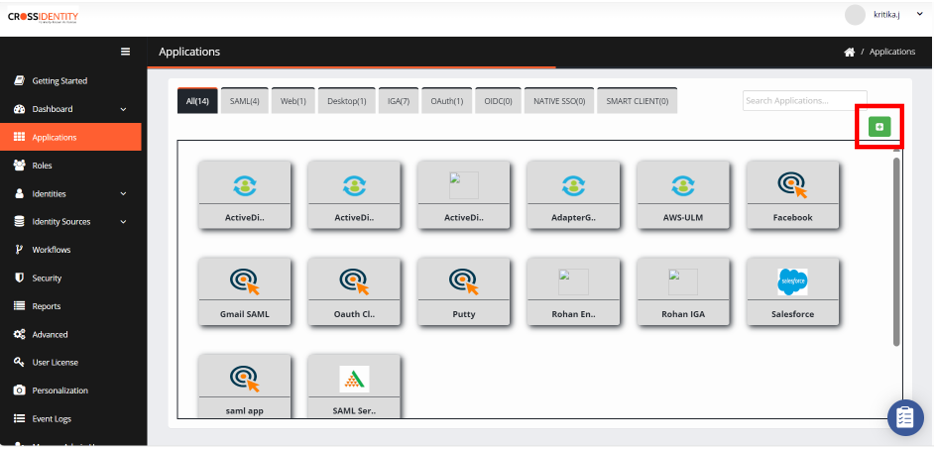
- To onboard the Azure AD provisioning application from the global app store, go to the Applications > click the ‘+’ symbol to add an application.
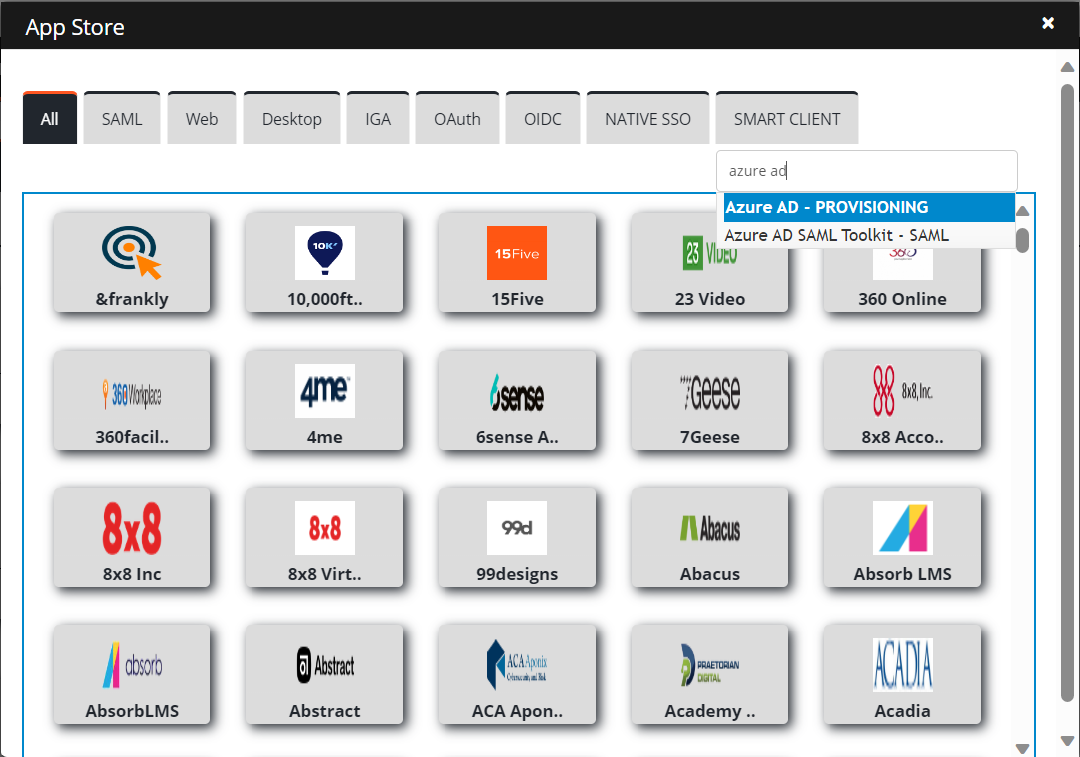
- In the AppStore pane, search the Azure AD application.
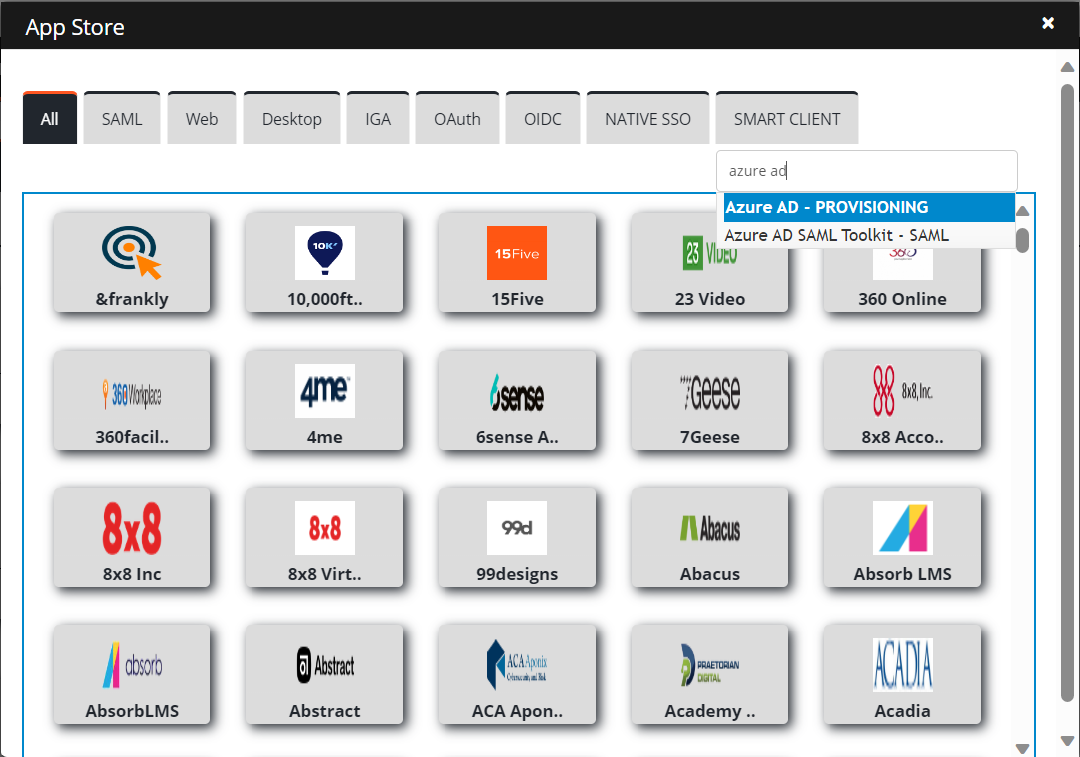
- Once it is displayed, click on it and it will take you to the application configuration window.
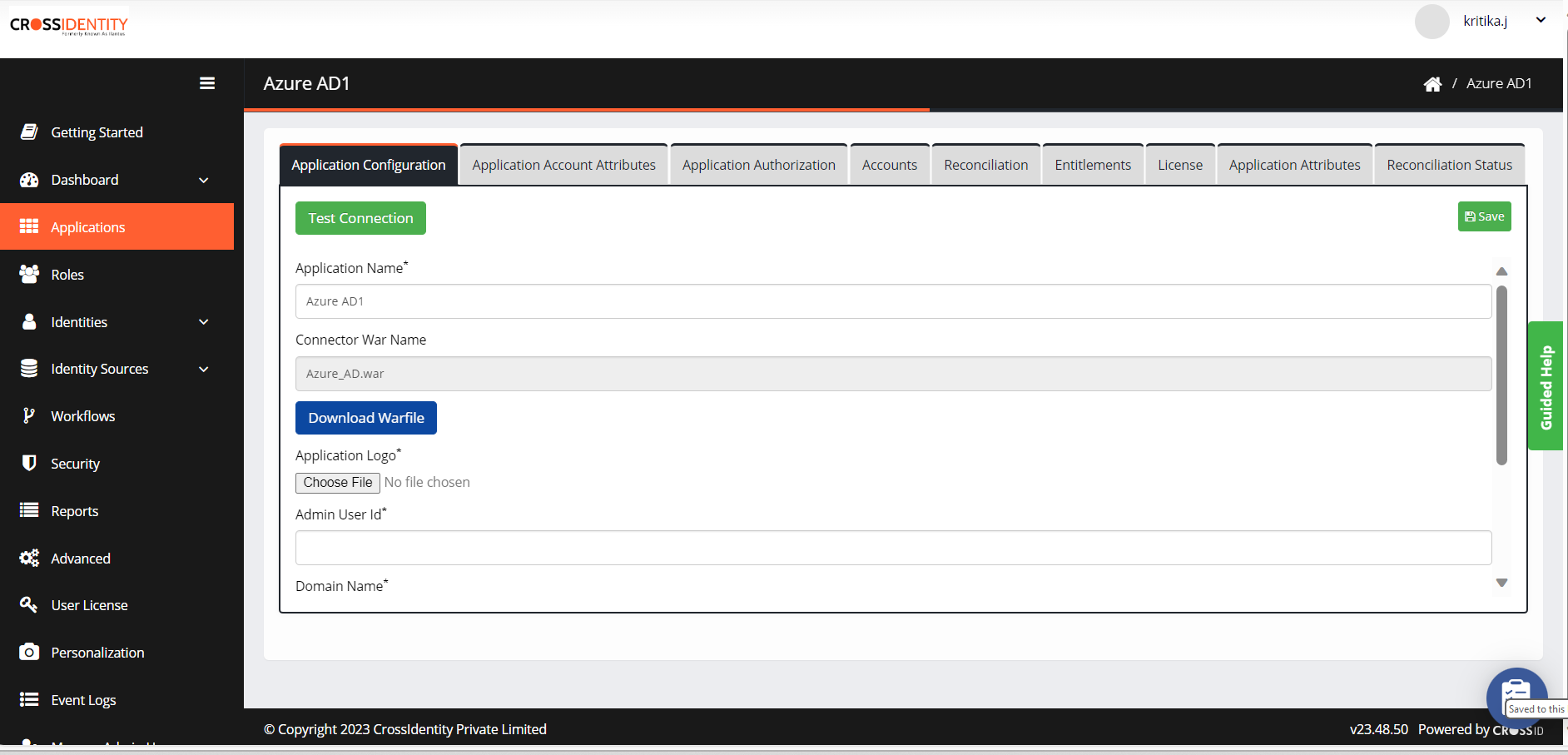
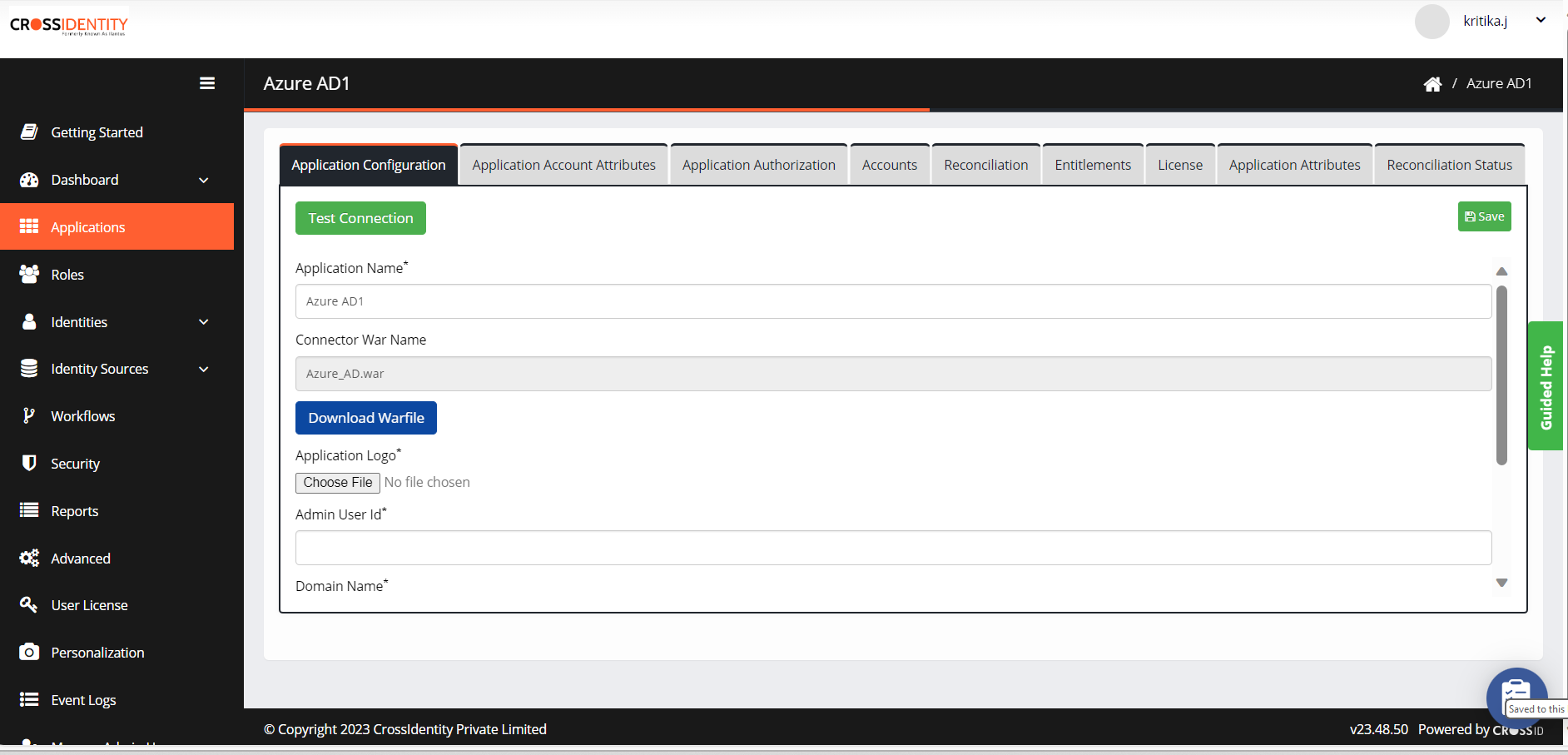
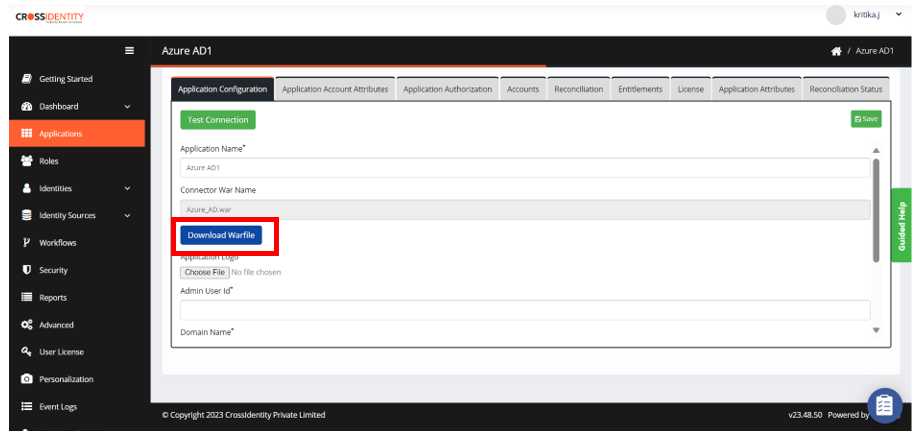
- Fill out the required details in the Application Configuration tab.
- Application Name: Provide a name. Example: AzureAD.
- Connector War name: This is an uneditable field. Example: AzureAD.war
- Application logo: Choose a logo for the application.
- Click Save.
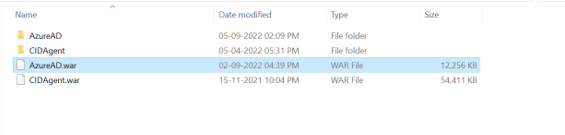
- Ensure that the Azure AD connector war file has been deployed in the agent webapps folder. C:\Program Files\Apache Software Foundation\Tomcat 9.0\webapps in this location.
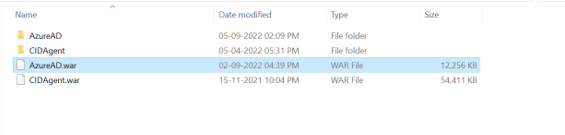
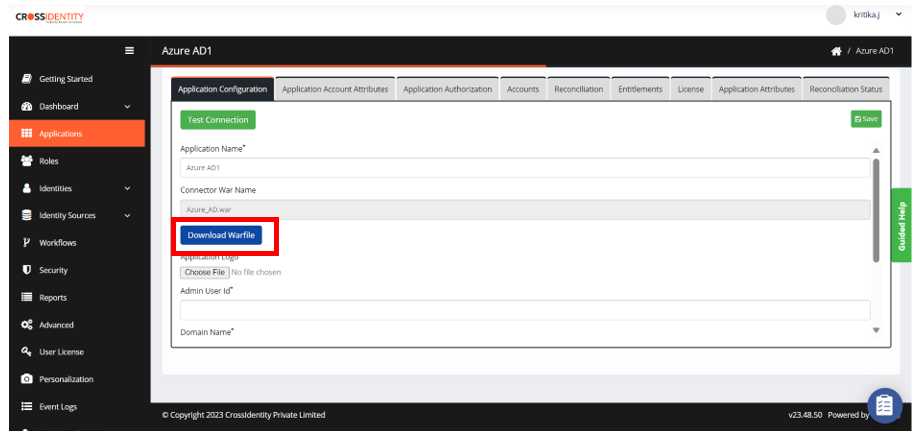
- If the AzureAD.war file doesn’t exist in the above location, download the war file from CI. (Go to Applications menu > Application Configuration tab > click on Download WarFile)
- Once the war file is downloaded, place it in C:\Program Files\Apache Software Foundation\Tomcat 9.0\webapps and restart the agent.
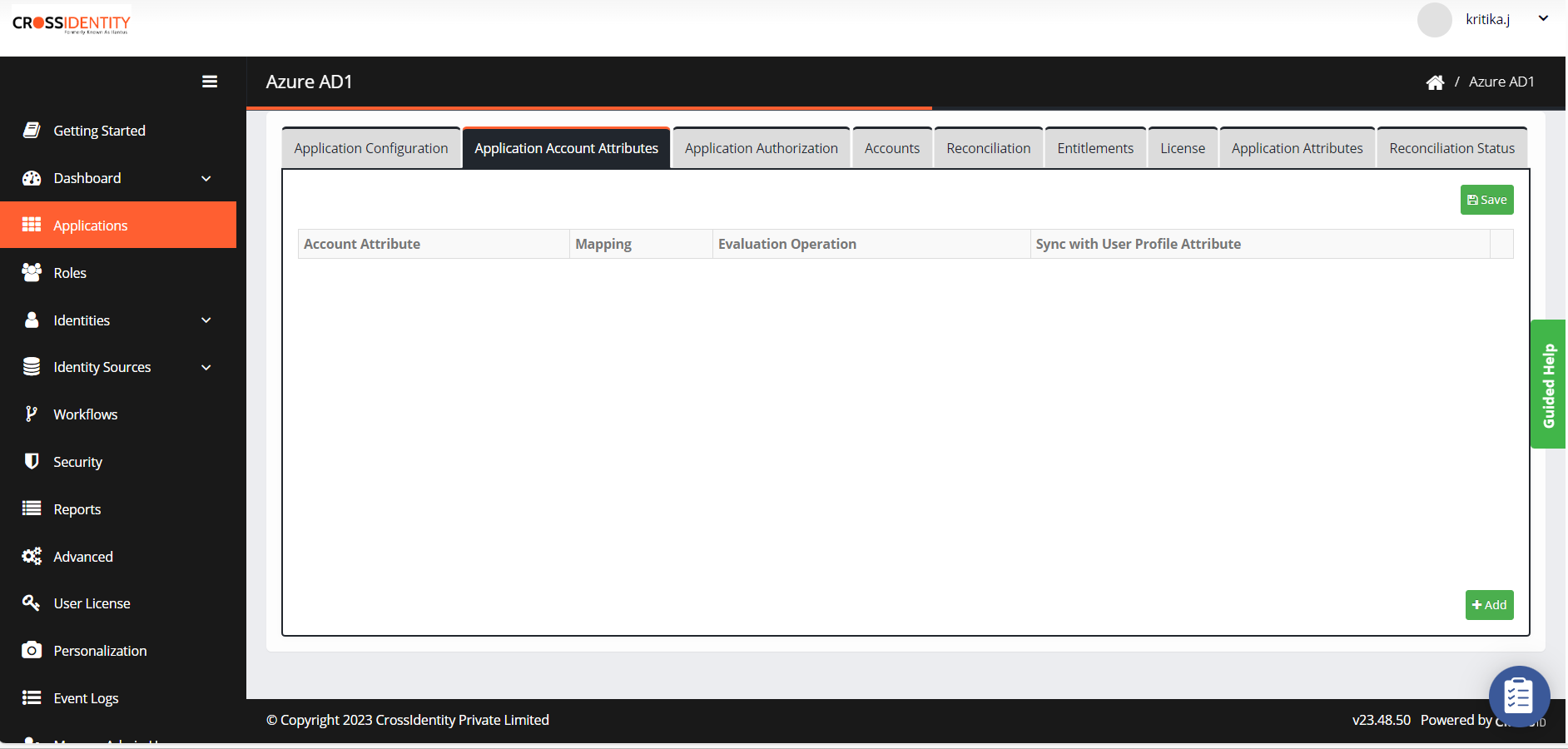
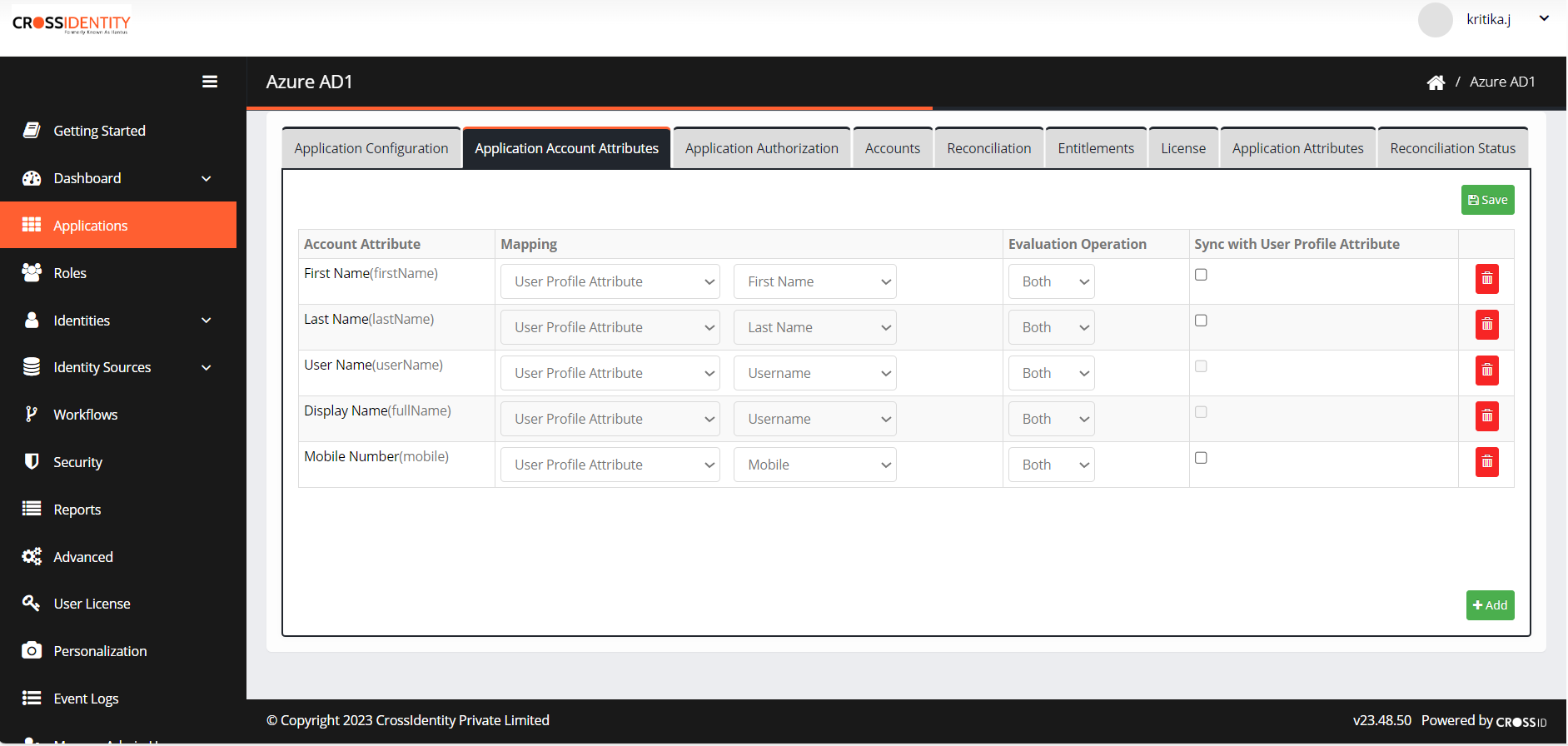
Application Account Attributes
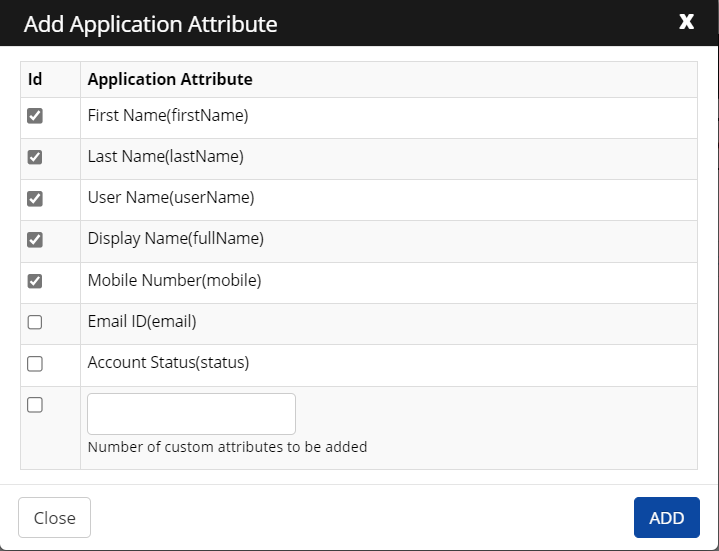
- Go to Application Account Attributes and click +Add.
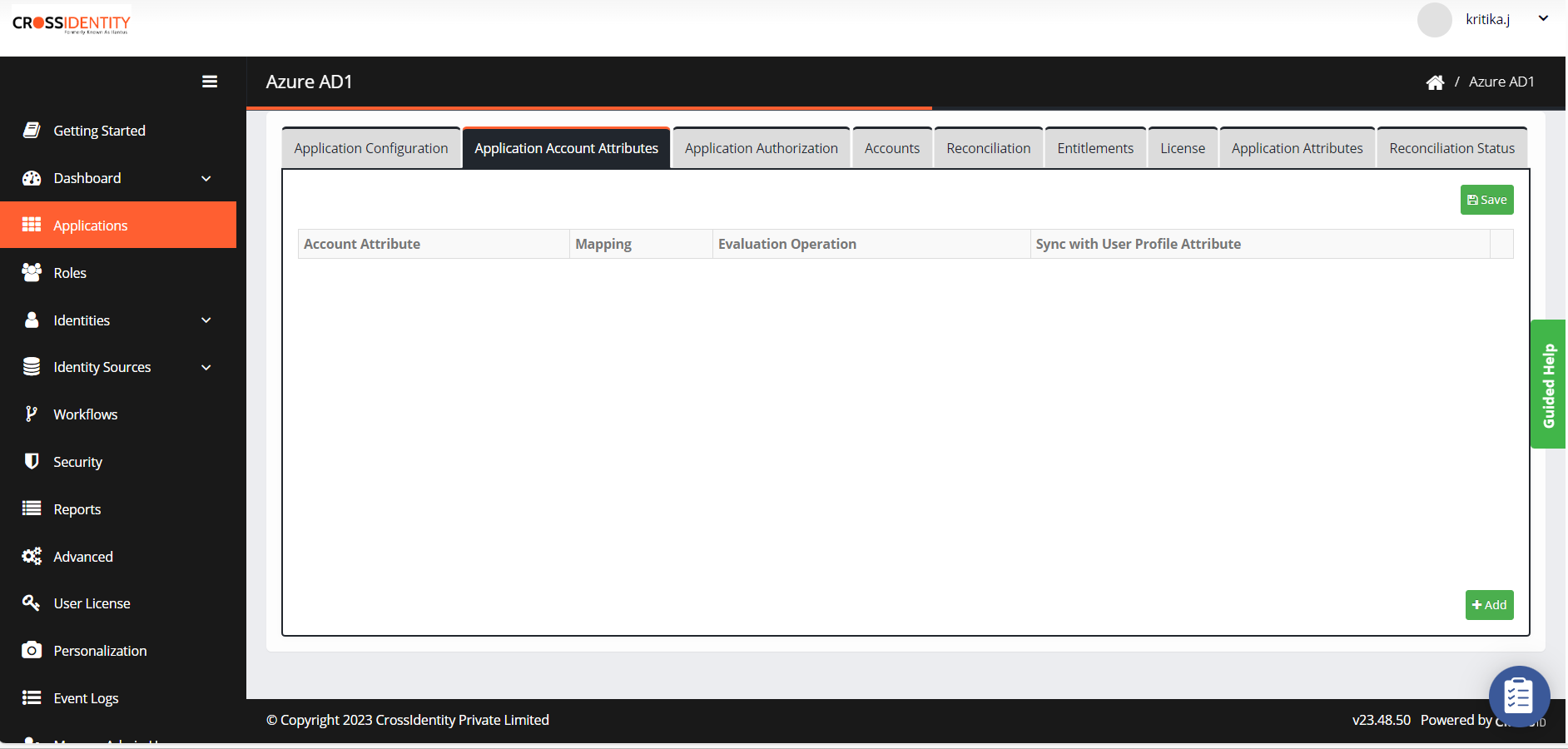
- Select the necessary attributes by checking the appropriate boxes and then click ADD.
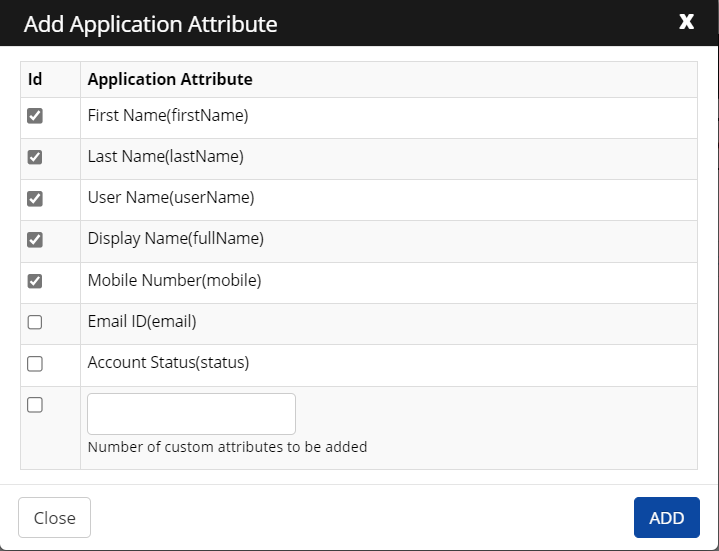
- On the next screen, you can see the added application account attributes and map the attributes as per requirement.
- Select the Mapping method from the drop-down.
- User Profile Attribute: When you choose this option, you need to define a user attribute that matches with Active Directory.
- Assigning Group to the user based on expression calculation from UI:
Groups can be assigned as per the business logic and the same is achieved by defining expressions in CI as shown below.
- Evaluation Operation: Select Create, Modify, and Both from the drop-down. It applies to a user account with the selected account attributes.
- Sync with User Profile Attribute: Check the box to sync account attributes from the target application to Cross Identity.
- Select the Mapping method from the drop-down.
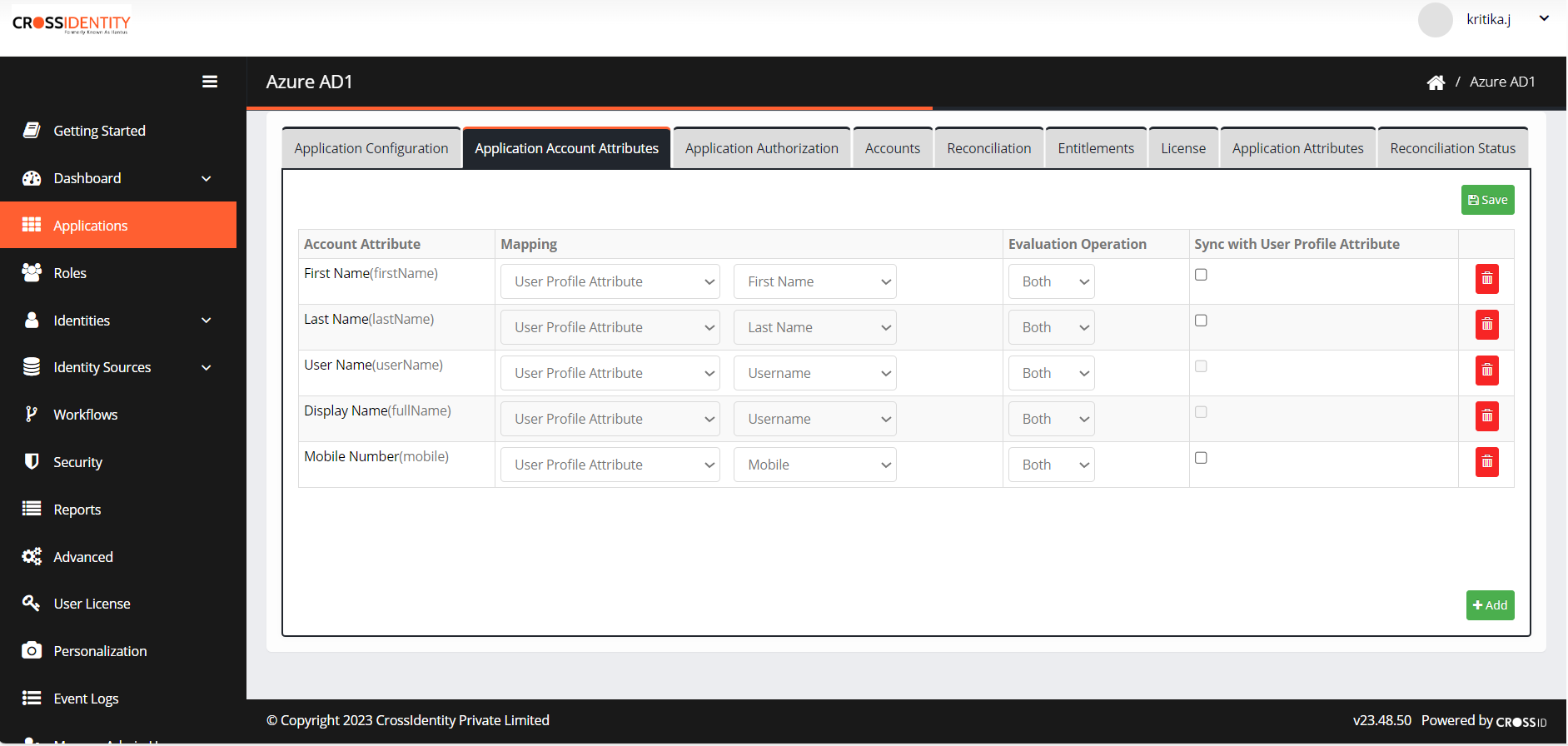
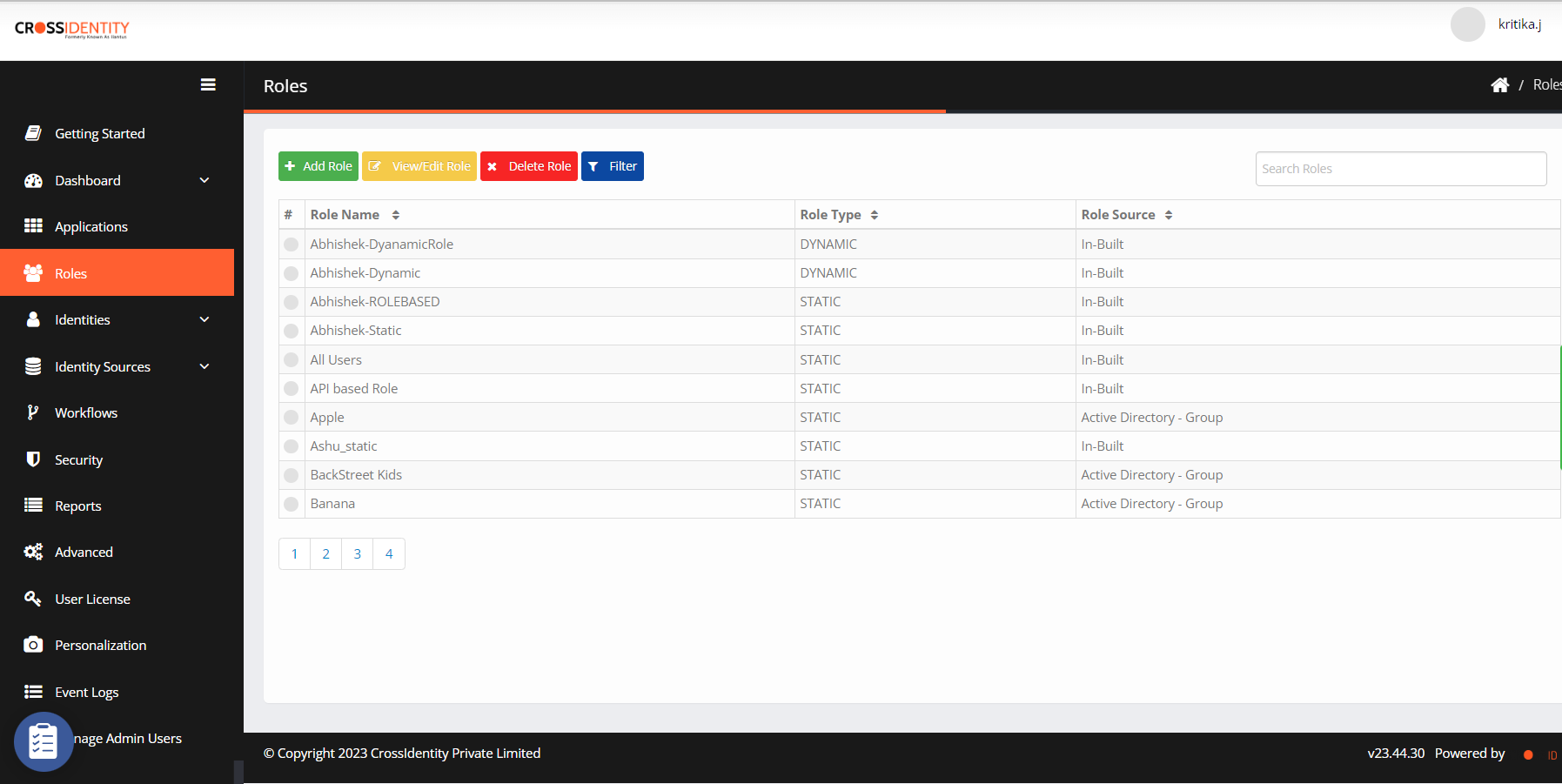
Add Roles in Cross-Identity
- Navigate to Roles from the menu.
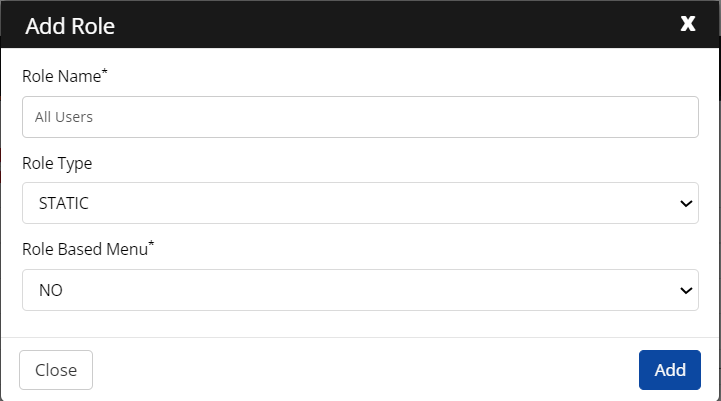
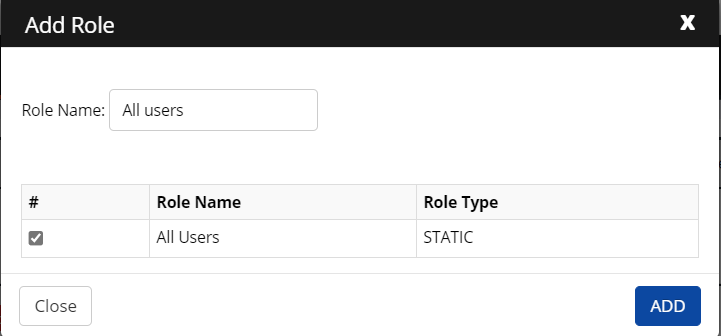
- Click Add Role. The Add Role screen appears.
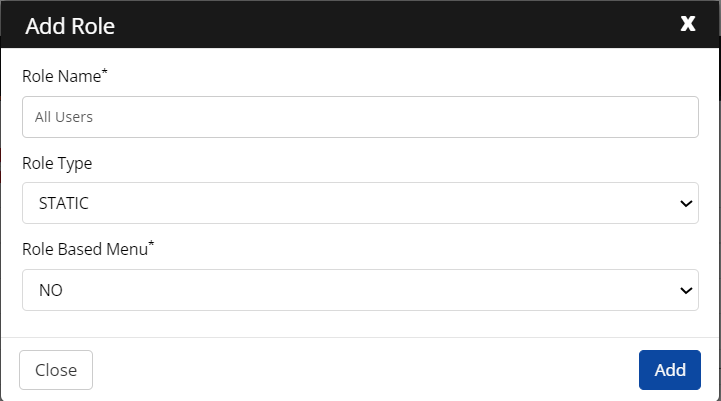
- Click ADD.
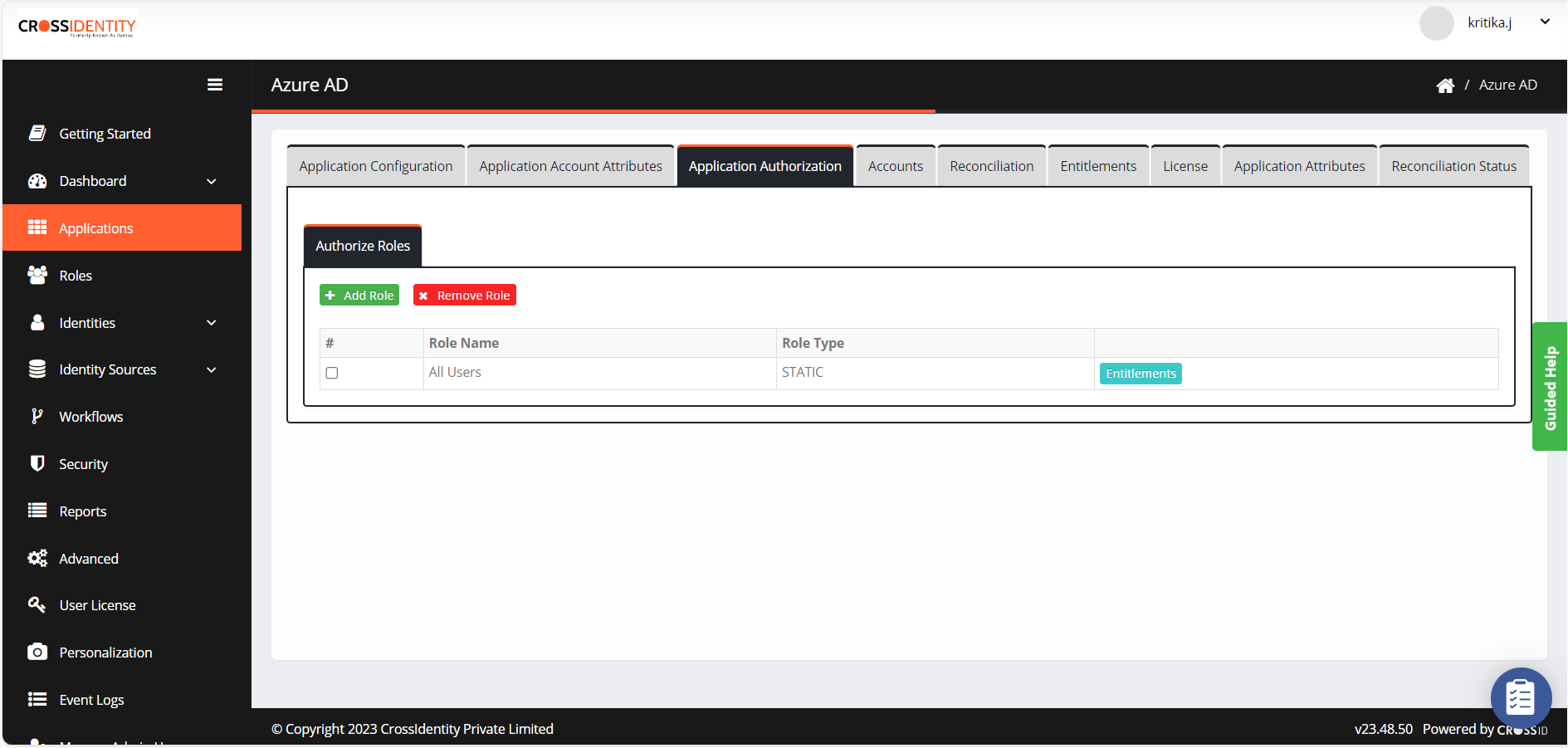
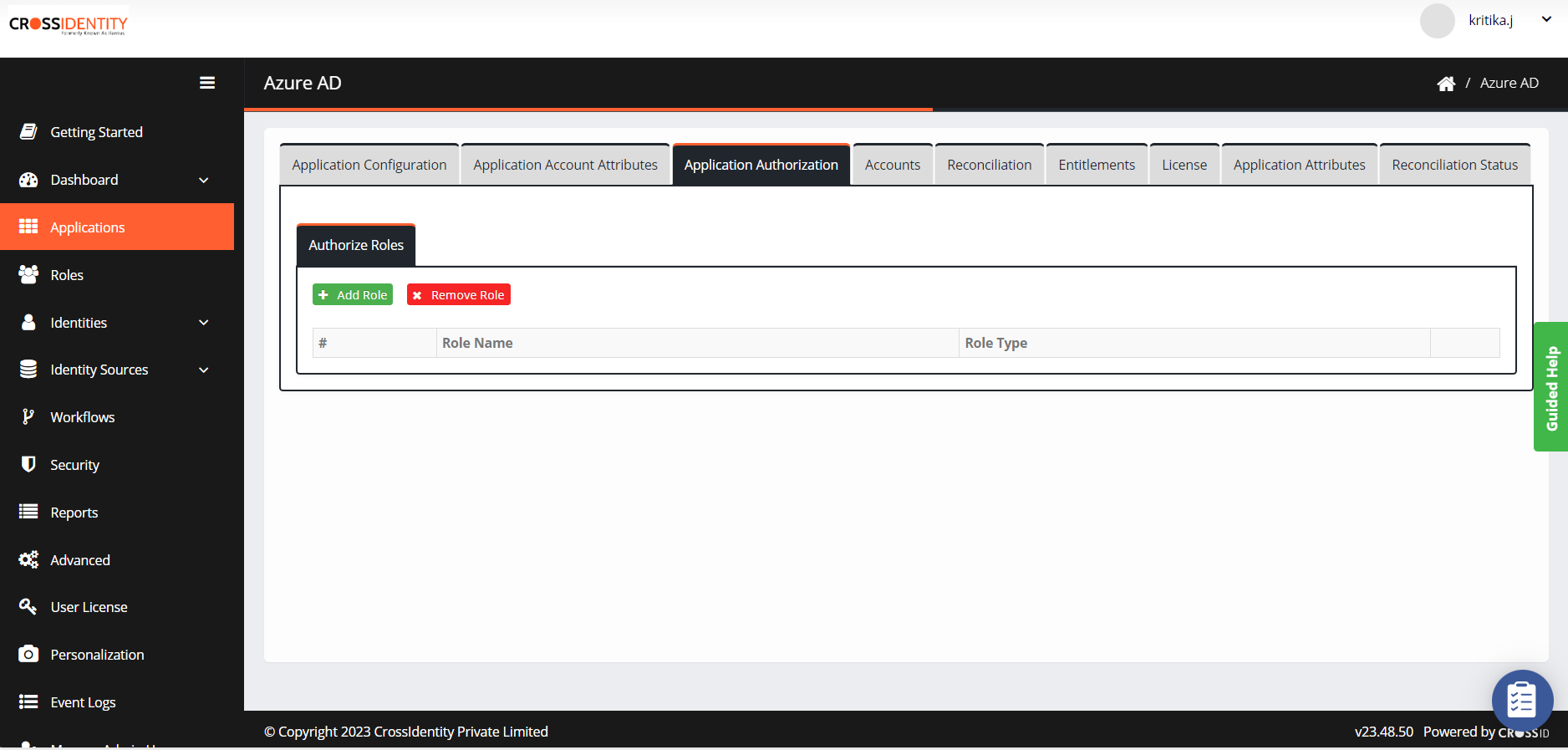
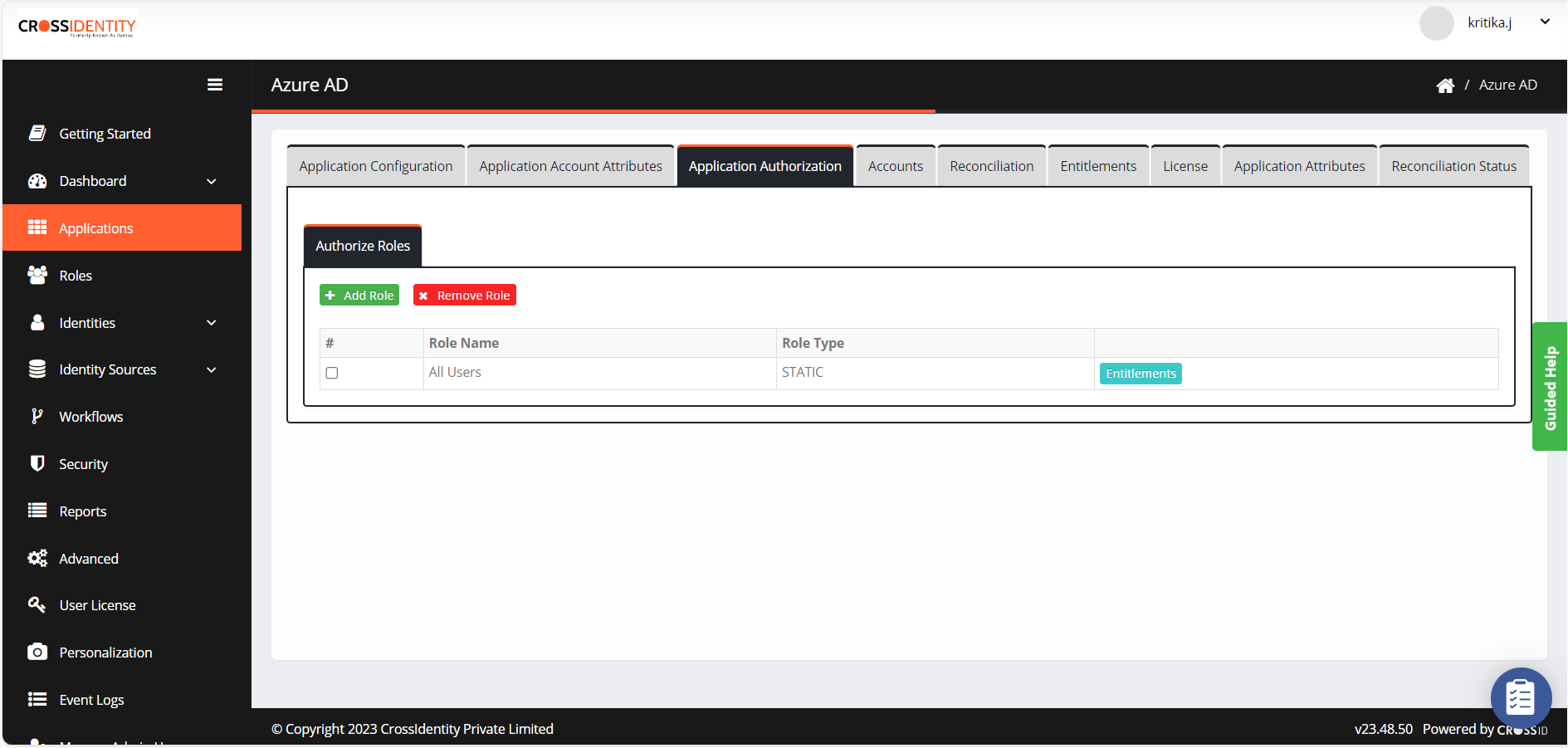
Application Authorization
- Navigate to Application Authorization. The application authorization screen is displayed.
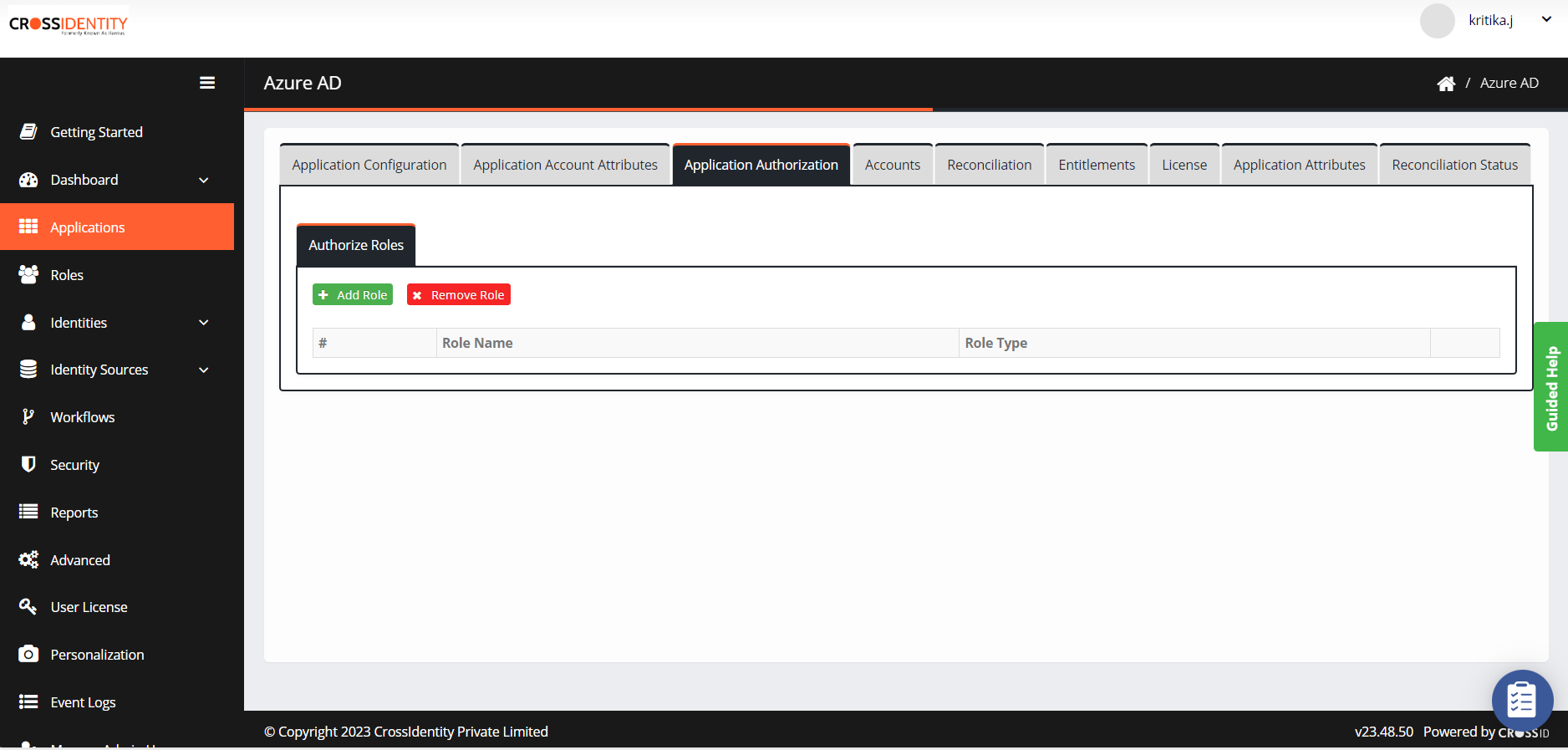
- Click Add Role and search for the role added in CI.
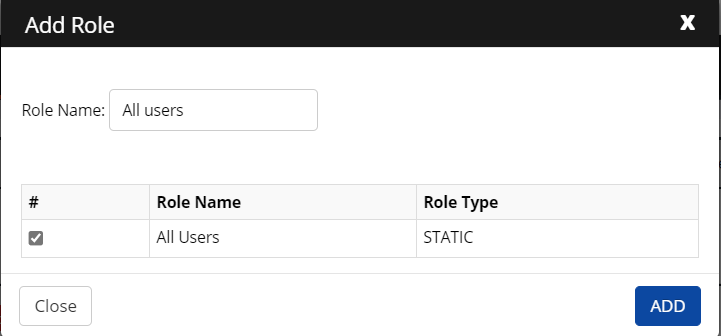
- Select the role and click ADD.
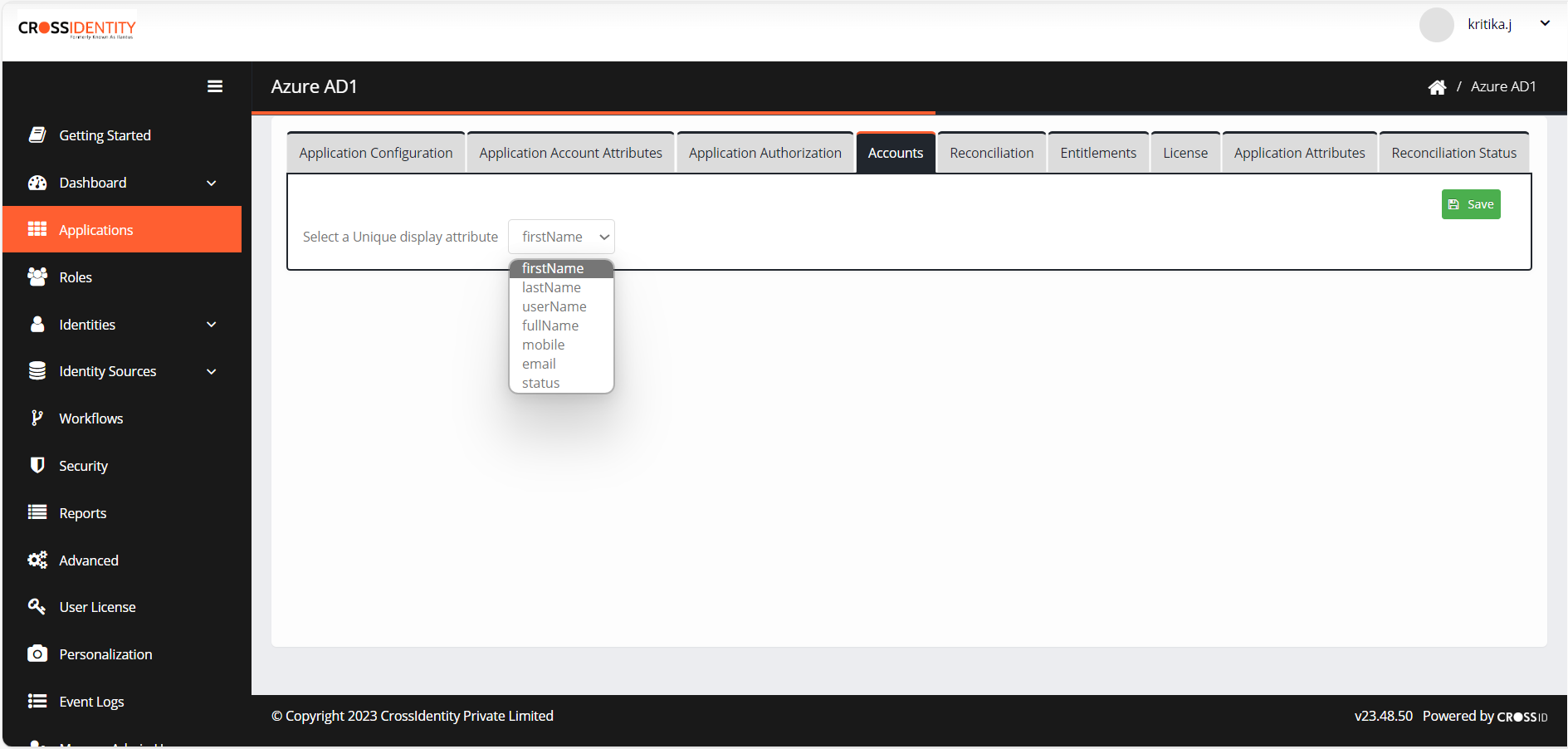
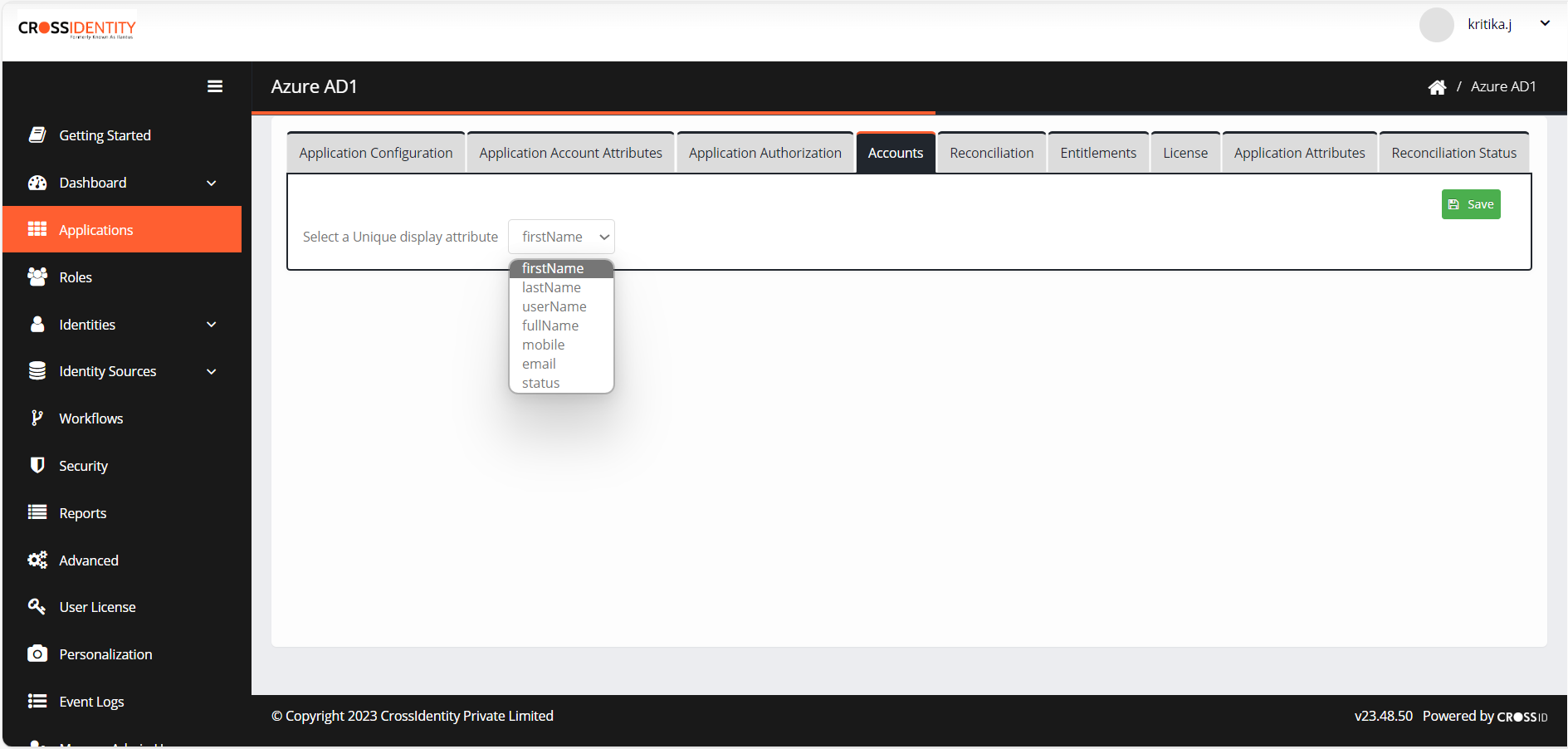
Accounts
- Navigate to Accounts.
- Select a unique attribute to link to identity and configure it as a display attribute.
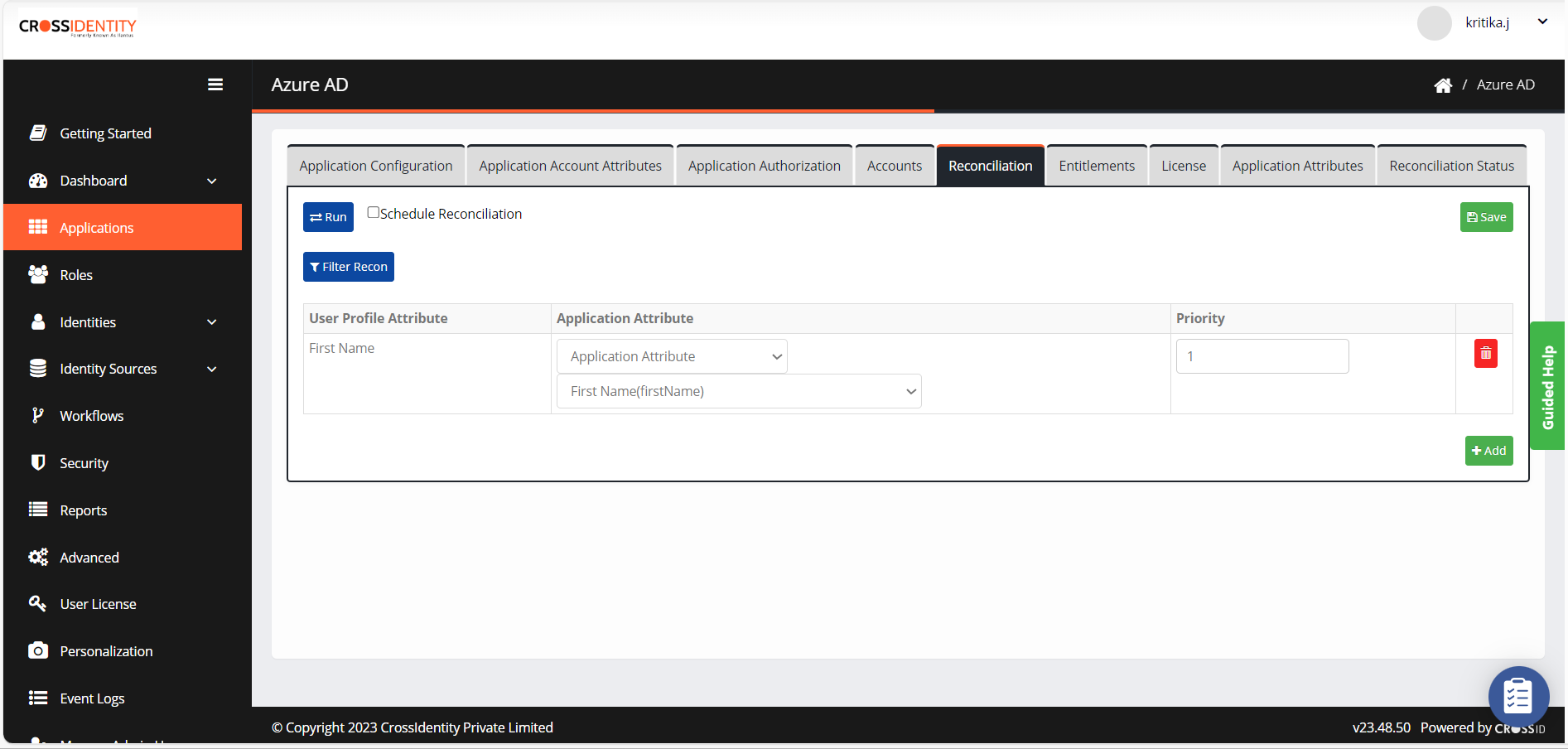
Reconciliation
The Recon rule is a must to link the CI identity and its respective account from the Target application using a unique link attribute (like email, employee ID, sAM account name, etc.). Multiple attributes can be considered by choosing the priority.
- Navigate to Reconciliation.
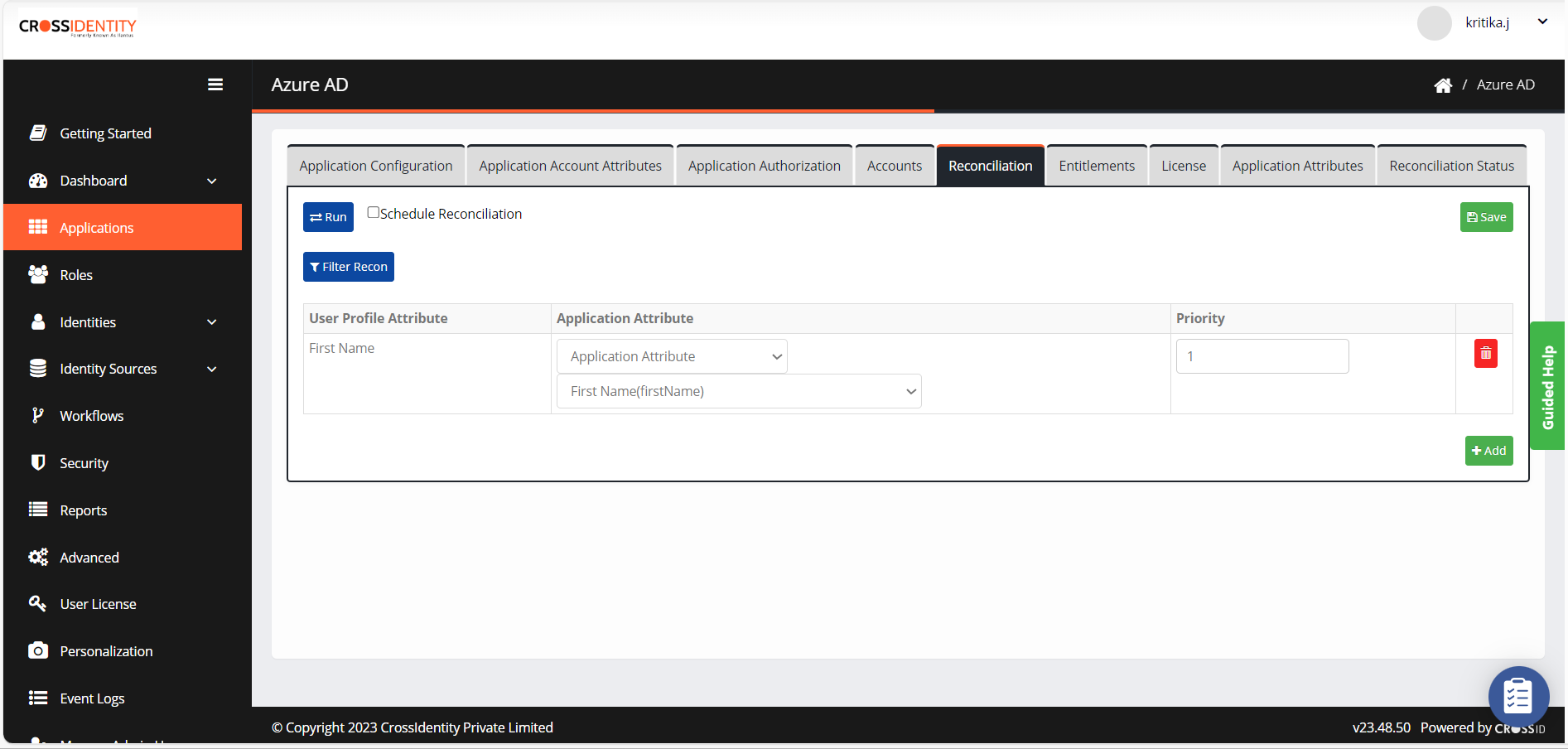
- Click Run to initiate the recon process.
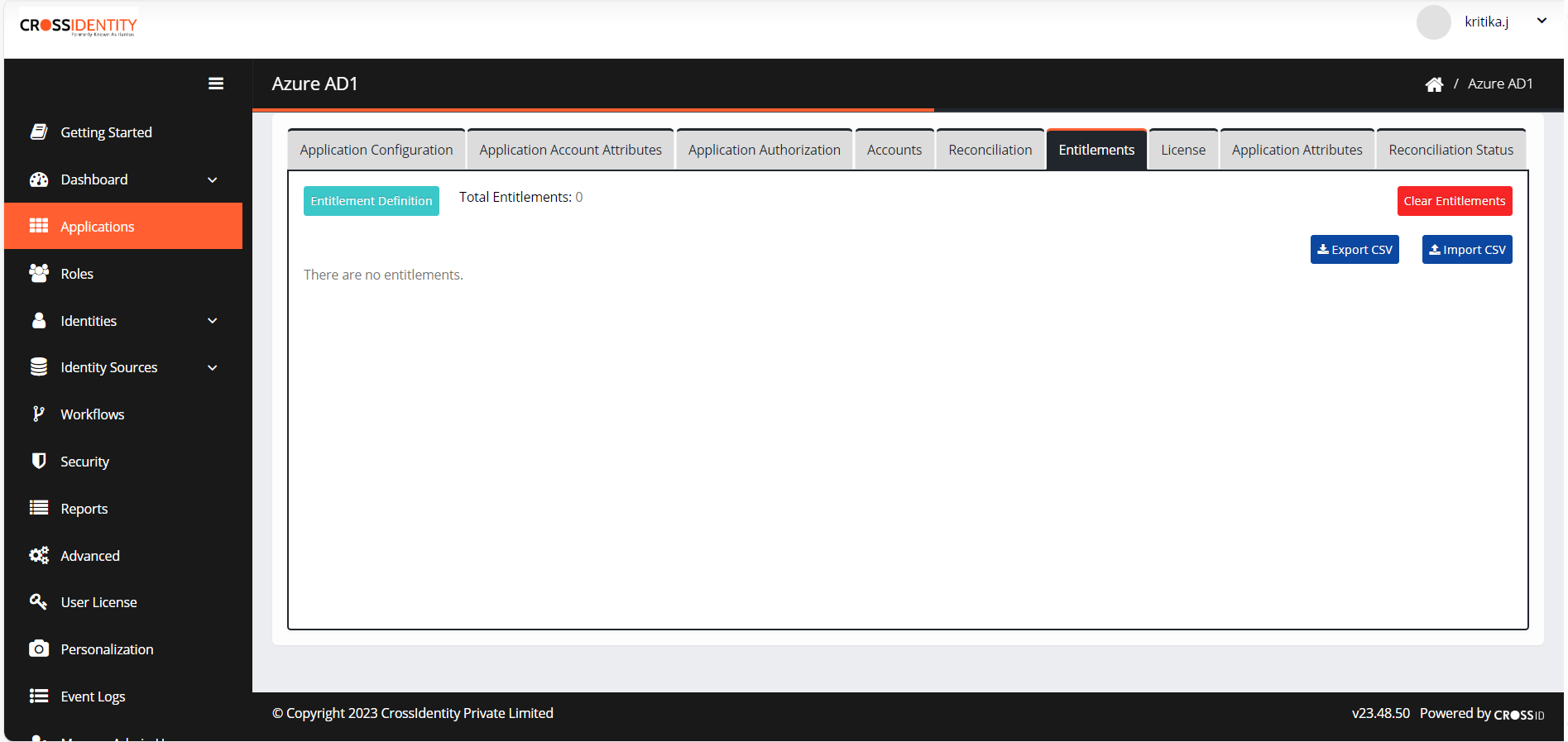
Entitlements
- Navigate to Entitlements.
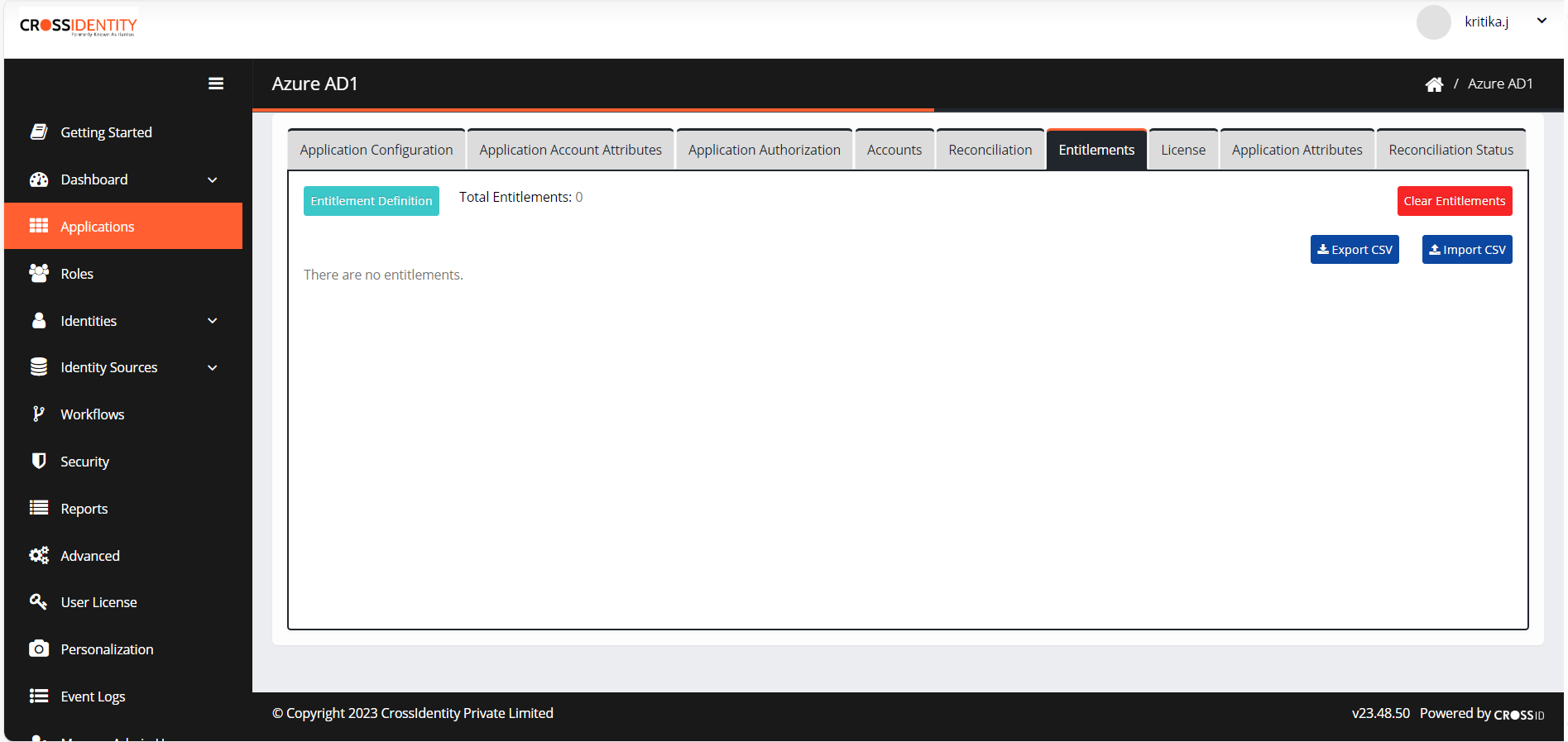
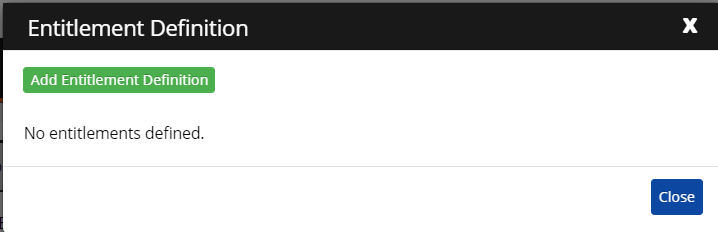
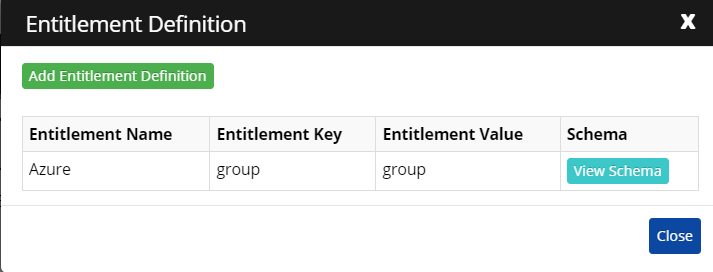
- Click Entitlement Definition > Add Entitlement Definition.
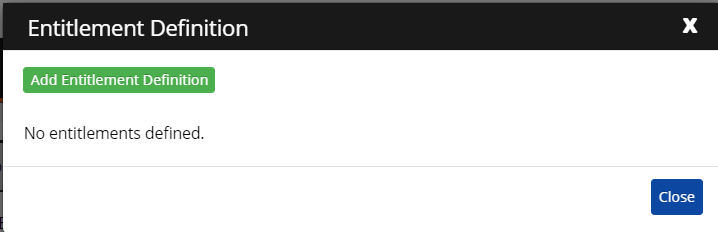
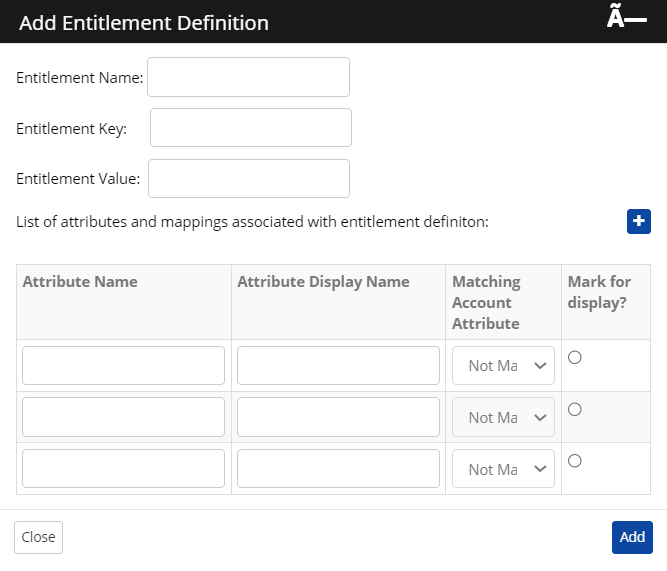
- Enter the following details in the dialogue:
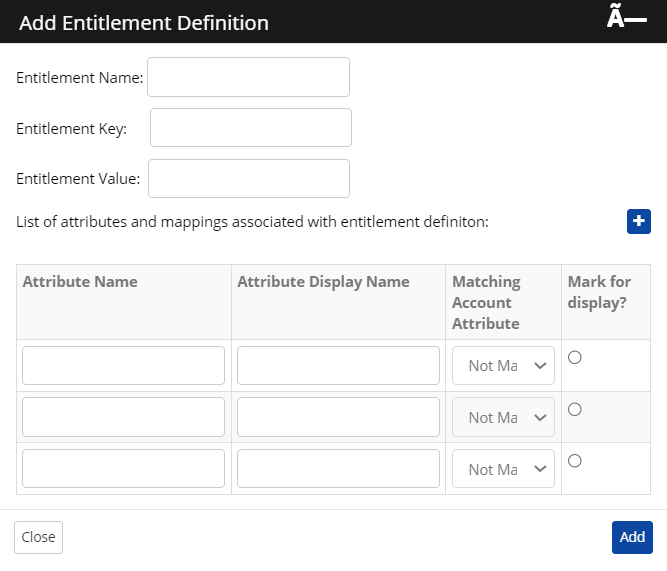
Sr. No. Entitlement Name Entitlement Key Entitlement Value 1. Azure (could be any user-friendly name) Group Group - The entitlement key and value are checked in the connector to fetch group details. As per the schema defined, the group names and their members are fetched and will be displayed in the entitlement tab.
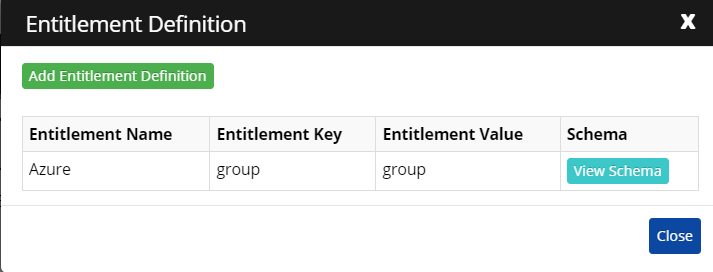
- Set schema details: In Connector, Attribute Name fields are used to fetch group names and members of that group from respective API responses. Attribute Display name is a user-defined display name. The mapped Attribute is mapped to the Display Name (as we are considering the Display Name as a unique key attribute) which represents the Group name, and the chosen will be displayed in the CI UI entitlement section.
Sr. No. Attribute Name Attribute Display Name
Mapped Attribute Marked Display 1 name groupName Display Name True 2 member member Display Name False

Was this article helpful?
.png)

.png)